The unfulfilled potential of Microsoft Flow connectors
Using custom connectors, you can integrate your business applications in Microsoft Flow. But the idea sounds better than the reality is.
Automate what can be automated
Many compare Microsoft Flow to IFTTT (If-This-Then-That). But it’s so much more than that. Using the tens of connectors and hundreds of templates, users without any development skills, can automate their daily work.
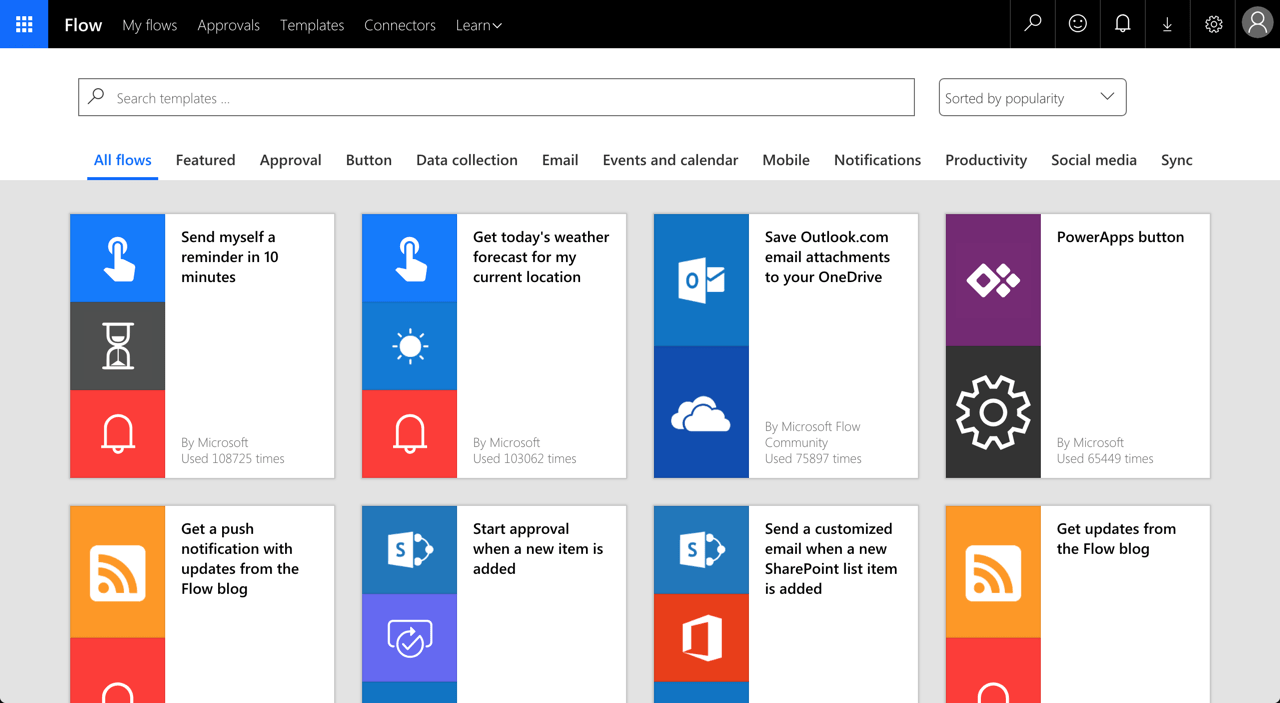
From simple action-reaction recipes, to a complete business processes with conditional executions, variables, web requests and scheduled executions: Microsoft Flow caters to all our needs.
The true benefit of Microsoft Flow
Unless you spend your day writing reports, creating presentations or crunching numbers in spreadsheets, you will need the ability to access your organization’s applications to automate your daily routine. Most likely, these applications are not among the standard connectors provided by Microsoft and third parties. But that’s not a problem at all! Microsoft Flow allows you to create custom connectors that allow you to integrate applications used in your organizations in your flows.
Custom Microsoft Flow connectors are extremely powerful and flexible. They allow you to connect to any API inside your organization or on the internet. Every user in your organization is allowed to create a custom connector and the only limitation is what they know… or what they read on the internet. Once they create a custom connector, they can decide with whom in your organization they want to share it and start building flows. And they don’t need anyone’s approval to do this.
Help prevent data loss in Microsoft Flow
Before you start using Microsoft Flow in your organization, you should setup a Data Loss Prevention (DLP) policy. This policy will help you prevent data loss from Microsoft Flow. Because Flow allows users to connect Microsoft’s applications, such as SharePoint or Outlook, with third-party applications, such as Slack or Twitter, a DLP policy allows you to choose which applications can be used together and are allowed to access the business data.
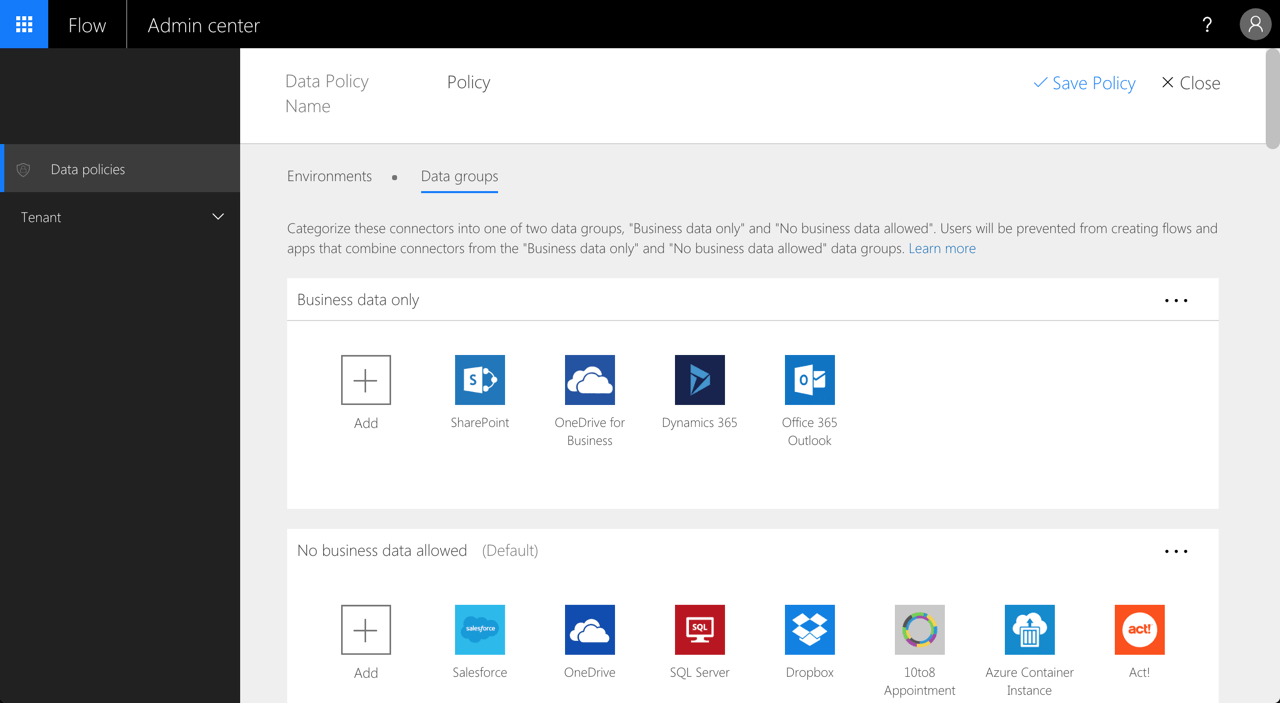
As your business data is stored in the Microsoft cloud, you will likely allow users to exchange it freely between applications that are a part of the Microsoft cloud, but will disallow the information to be shared with third-party applications.
Default is what you get
When configuring a DLP policy in your tenant, a part of the configuration is specifying the default data group: Business data only or No business data allowed. While the name is indicative and by itself doesn’t impose any limitations, users building flows won’t be able to use applications from two different groups in the same flow. And here is the catch.
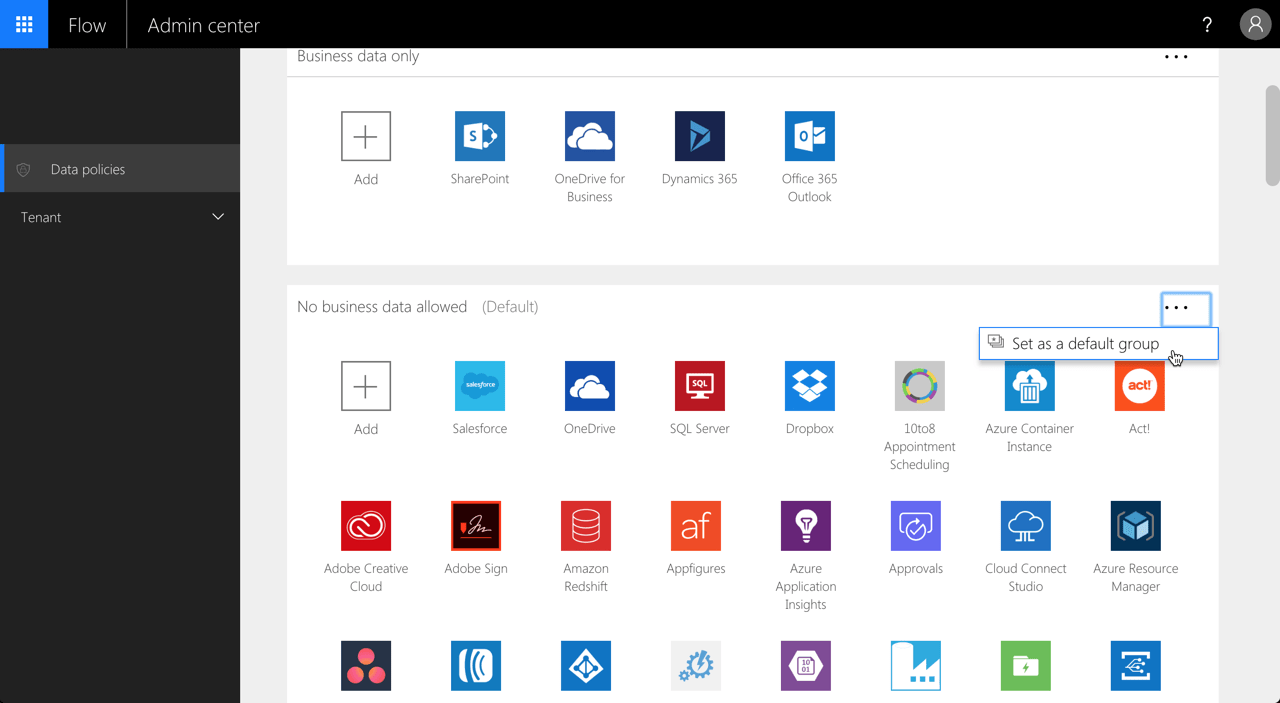
From the information security point of view, you would do good to set the No business data allowed group as the default data group in your DLP policy. When you create a custom connector, it’s automatically assigned to the default group. And that’s exactly what you want. Since each connector can connect to any API on the internet, you want to control which connectors have access to your business data and where the data can potentially be sent to. But… at this moment, there is no way for you to assign a custom connector to a different data group. It is always assigned to the default group.
No easy choice
So in the end you’re left with a choice, and you lose either way. Do you set the Business data only group as default so that your organization can integrate its line of business application with Microsoft Flow and risk your data leaving your organization’s premises? Or do you set the No business data allowed group as default instead, to ensure that your business data is secure and prevent your users from automating their work risking them potentially turning to shadow IT practices to get their job done?
It could’ve been so much more
When you think about it, the ability to control to which data group a custom connector is assigned, is a prerequisite for an organization to use Microsoft Flow securely and benefit of its extensibility capabilities. Unfortunately, such configuration is not possible at this moment. The good news is, that Microsoft is aware of this limitation and will provide us with the ability to assign custom connectors to data groups in a DLP policy in the future. We don’t know when yet and so for now, this promise of a better future will have to do as we choose for the lesser evil.